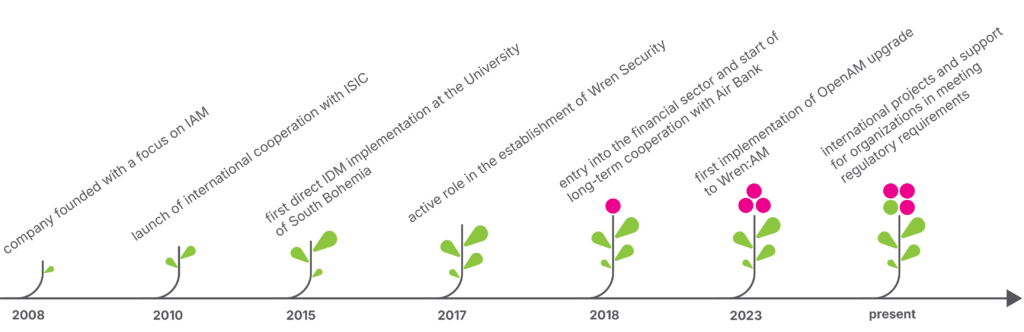
In February this year, we mark 18 years since the founding of Orchitech. Since 2008, we have specialized in Identity & Access Management (IAM) — the governance of digital identities and access rights. While this domain was already important at the time of our founding, it has evolved significantly over the years.
Today, identities are no longer just “accounts in a system.” They have become the central pillar of security, compliance, and day-to-day operations within modern organizations.
How Identity & Access Management Has Evolved Over 18 Years
When we started in 2008, organizations were already addressing user account management, access rights, and directory integrations. At the time, IAM primarily meant provisioning, account synchronization, and basic auditability.
Over time, however, the scope of IAM has expanded considerably.
Today, IAM encompasses:
- Identity lifecycle management (joiners, movers, leavers)
- Identity governance and regular access recertification
- Audit trails and traceability of changes
- Integration of cloud and SaaS services
- Customer identity management
- Support for regulatory compliance
With the rise of cloud computing, hybrid environments, and modern security approaches such as zero trust, identity has become the central element of security architecture. Without control over identities and access rights, organizations cannot fully control their risk exposure.
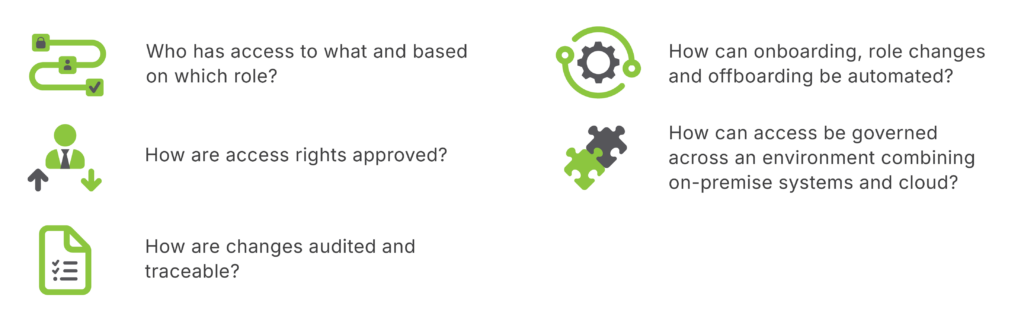
What IAM Solves in Practice
Projects Across Industries
Over the past 18 years, we have delivered IAM projects across a wide range of industries — from public administration and universities to telecommunications, banking, and healthcare.
Each sector comes with its own specifics: regulatory frameworks, data sensitivity levels, and operational cultures. Yet the common denominator remains the same: the need for clearly defined responsibilities, transparent approval processes, and a sustainable long-term access governance model.
IAM is not an isolated IT initiative. It impacts HR, security, internal audit, and executive management. The integration of technology with well-designed processes is often the decisive factor in project success.
ISIC: A Global Identity Platform
One of our longest-standing engagements is our more than 15-year collaboration with the global headquarters of ISIC, the International Student Identity Card organization. We manage its global identity platform serving more than 20 million cardholder identities and connecting national partners across dozens of countries.
Such a solution must operate seamlessly across legal jurisdictions, integration interfaces, and time zones. It requires scalability, high availability, and long-term technological continuity.
Continuity is particularly critical in the identity domain. Identity infrastructure is not a short-term project, but a foundational component of an organization’s digital ecosystem.
Wren Security and Technological Continuity
A significant milestone in our development was our active role in the creation and advancement of the Wren Security platform, which builds upon open-source products such as OpenIDM and OpenAM, originally maintained by ForgeRock.
Following the discontinuation of their development, many organizations faced the challenge of ensuring continuity and further evolution of their identity environments. Wren Security (Wren:IDM, Wren:AM, Wren:ICF, Wren:DS, and Wren:IG) represents a modern open-source solution that provides this continuity.
At Orchitech, we support organizations using OpenAM or OpenIDM in executing a controlled and seamless transition to the Wren Security platform.
Long-term sustainability (both technological and economic) is essential in IAM. Identity solutions must remain reliable not only today, but for years to come.
NIS2, Audit, and Today’s Regulatory Landscape
In recent years, regulatory requirements have intensified, including the European NIS2 Directive.
For many organizations, this has become a catalyst for systematically strengthening access governance, particularly in terms of audit trails, access approvals, and clear allocation of responsibilities.
A well-designed IAM solution does more than ensure compliance. It simplifies daily operations, reduces manual interventions, and mitigates operational risk.
Orchitech Milestones
18 Years of Experience — and Looking Ahead
Over the past eighteen years, Identity & Access Management has undergone a profound transformation. Not because identity was previously unimportant, but because its significance has expanded from technical account administration to a strategic discipline at the core of risk management, security, and compliance.
Our ambition remains the same: to help organizations build identity infrastructures that are secure, auditable, and sustainable in the long term.
Because today, identity is no longer a detail of IT architecture.
It is its foundation.
